We Take CDP Security Seriously
You don’t compromise on your customers’ data security, and neither do we. Our processes, behaviors, and every level of our infrastructure are built with enterprise security in mind. Because we serve the world’s largest, globally distributed, technologically mature companies, we built a customer data platform (CDP) that stands up to the toughest CISO scrutiny.Compliance
SOC 2 Type 2
Treasure Data undergoes an annual SOC 2 Type 2 audit covering the Security, Confidentiality, Availability, and Processing Integrity (PI) Trust Services Criteria (TSC).
Get a copySOC 3
Treasure Data undergoes an annual SOC 3 Type 2 audit covering the Security, Confidentiality, Availability, and Processing Integrity (PI) Trust Services Criteria (TSC).
Get a copyISO/IEC 27001
Treasure Data undergoes an annual ISO27001:2022 certification audit over the ISMS that governs the Treasure Data CDP.
Get a copyISO 27701
Treasure Data undergoes an annual ISO/IEC 27701:2019 certification audit over the PIMS that governs the Treasure Data CDP.
Get a copyISO/IEC 27017
Treasure Data undergoes an annual ISO/IEC 27017:2015 certification audit over the ISMS that governs the Treasure Data CDP.
Get a copyISO/IEC 27018
Treasure Data undergoes an annual ISO/IEC 27018:2019 certification audit over the ISMS that governs the Treasure Data CDP.
Get a copyHIPAA Type 2
HIPAA compliance ensures that Treasure Data protects the confidentiality, integrity, and security of ePHI for our healthcare and life sciences customers. Treasure Data undergoes an annual HIPAA Type 2 audit to verify all HIPAA Security Rule requirements are addressed and operating effectively.
Get audit reportCSA STAR Level 1
CSA Star Level 1 is a self attestation intended for Cloud Service Providers (CSPs) that validates Treasure Data’s use of industry-leading best practices to secure data in our CDP.
Get a copyPrivacy Mark
Treasure Data undergoes annual PrivacyMark compliance audits. PrivacyMark is a privacy-centric certification in Japan that focuses on enhancing consumers’ awareness of personally identifiable information (PII) protections. The requirements are based on JISQ standards and are governed by JIPDEC (Japan Institute for Promotion of Digital Economy and Community). PrivacyMark is viewed as the Japan equivalent of the ISO/IEC 27001.
Get a copyFISC
Treasure Data has developed a guide to help our customers understand how our control environment aligns with the Center for Financial Industry Information Systems (FISC) guidelines. Many of the controls outlined in our guide are already implemented as part of existing third-party audited compliance offerings, such as our ISO/IEC 27001 certification and SOC 2 Type 2 report.
Get a copyPlatform security
Customer data encryption
Customer data protections
API security
Service availability
Penetration testing
Security monitoring and response
Security monitoring and response
Treasure Data’s administrative activity within the infrastructure is ingested and monitored within Treasure Data’s Security Incident Event Monitoring (SIEM) tool. Follow-the-sun coverage is in place to monitor SIEM alerts and activity.
Learn moreData localization
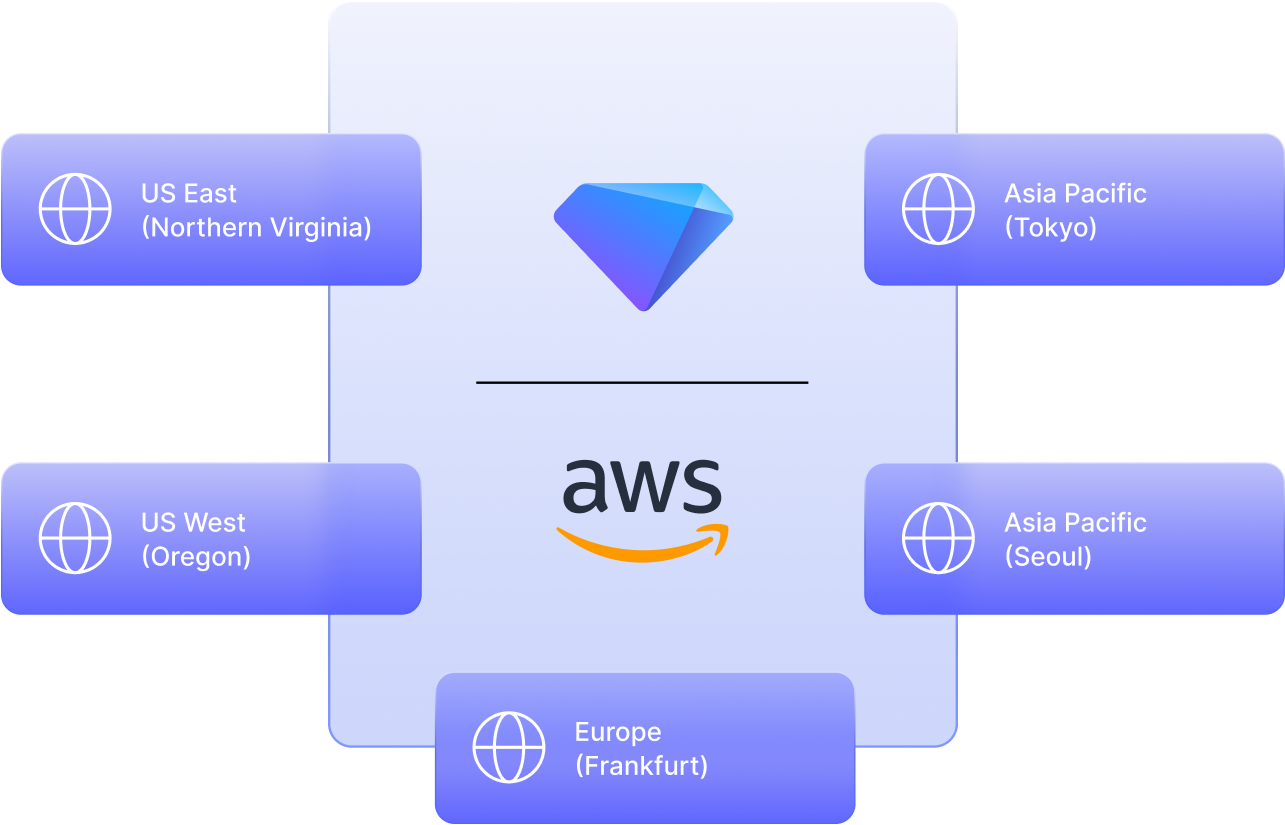
All infrastructure and storage services run within regional AWS data centers and leverage multiple Availability Zones. Treasure Data uses the following AWS regions:
-
US East (Northern Virginia)
-
US West (Oregon)
-
Europe (Frankfurt)
-
Asia Pacific (Tokyo)
-
Asia Pacific (Seoul)
Beyond compliance: Our approach to security
Consumer data is gold and should be as safe and secure as any precious material.
Learn about how our comprehensive approach to security and privacy goes beyond compliance, helping global brands gain trust and see business value.








